Merchant-initiated login
This flow should not be used on webpages or within mobile apps. For those scenarios, refer to Log in from websites or Login from a mobile app.
In the Merchant-initiated login flow, a merchant's system or machine triggers a Vipps/MobilePay login.
This supports special cases where there is no browser or app. For example:
- Log-in directly from merchant systems (e.g. point of sales systems or call-center solutions) based on phone number
- Log-in directly from machines and vending machines based on phone number
This is available for all Login-enabled clients, but to ensure a consistent user experience, this flow is not allowed on webpages and in apps; thus, log-in can't be done in the user's browser.
The process
In this flow, the merchant's system triggers the authentication/registration using the user's mobile number.

This triggers a push message from the user's Vipps or MobilePay app. By clicking the push message, the user is taken to their Vipps or MobilePay app to confirm the authentication/registration.
If the user hasn't enabled push from Vipps or MobilePay, they need to manually open the app and possibly pull the home screen down for a refresh to receive the authentication request.
If the user hasn't already consented to share information with a merchant, such consent will be required.
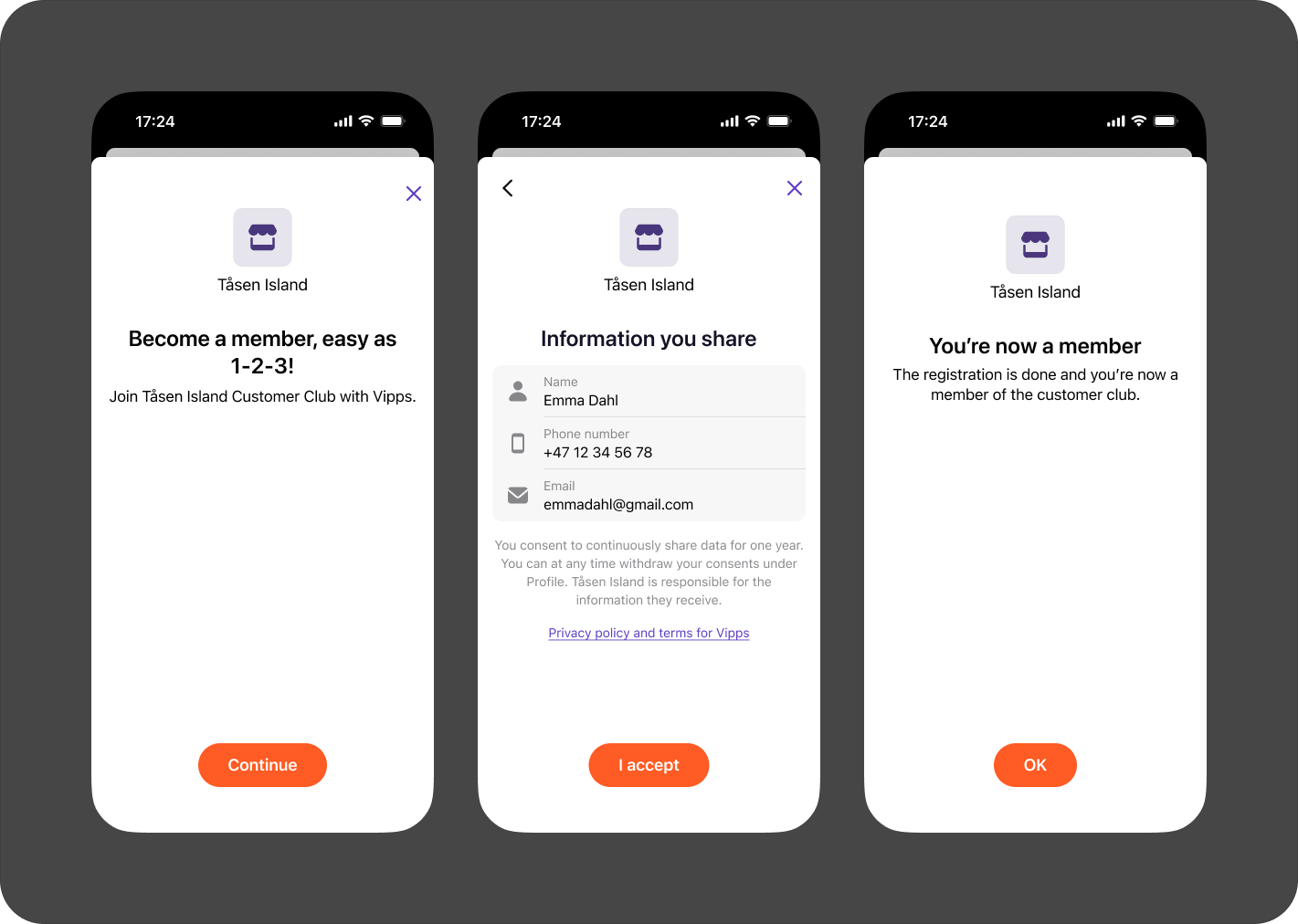
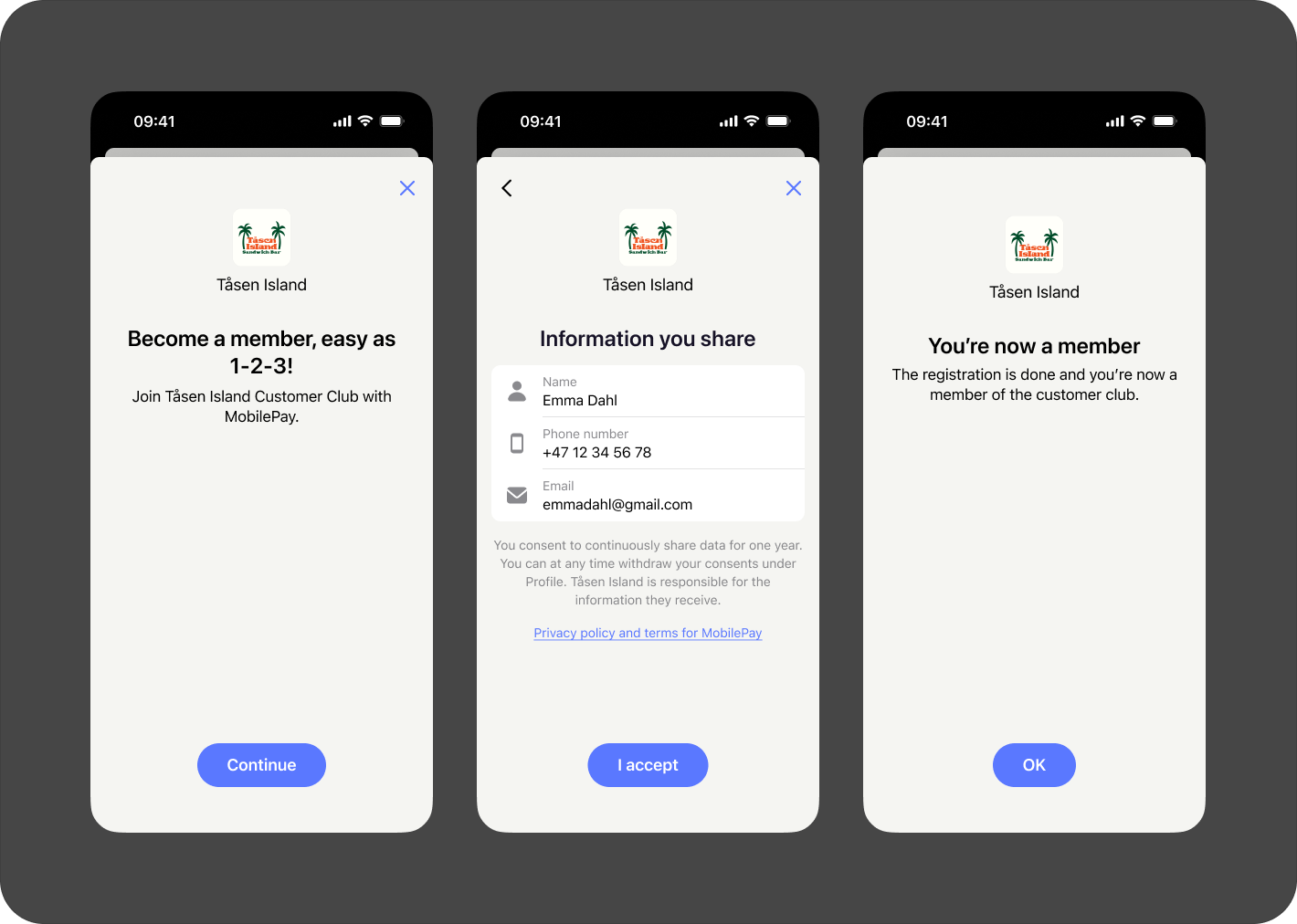
The merchant controls whether the user should get the confirmation of completion in the Vipps or MobilePay app. For example:
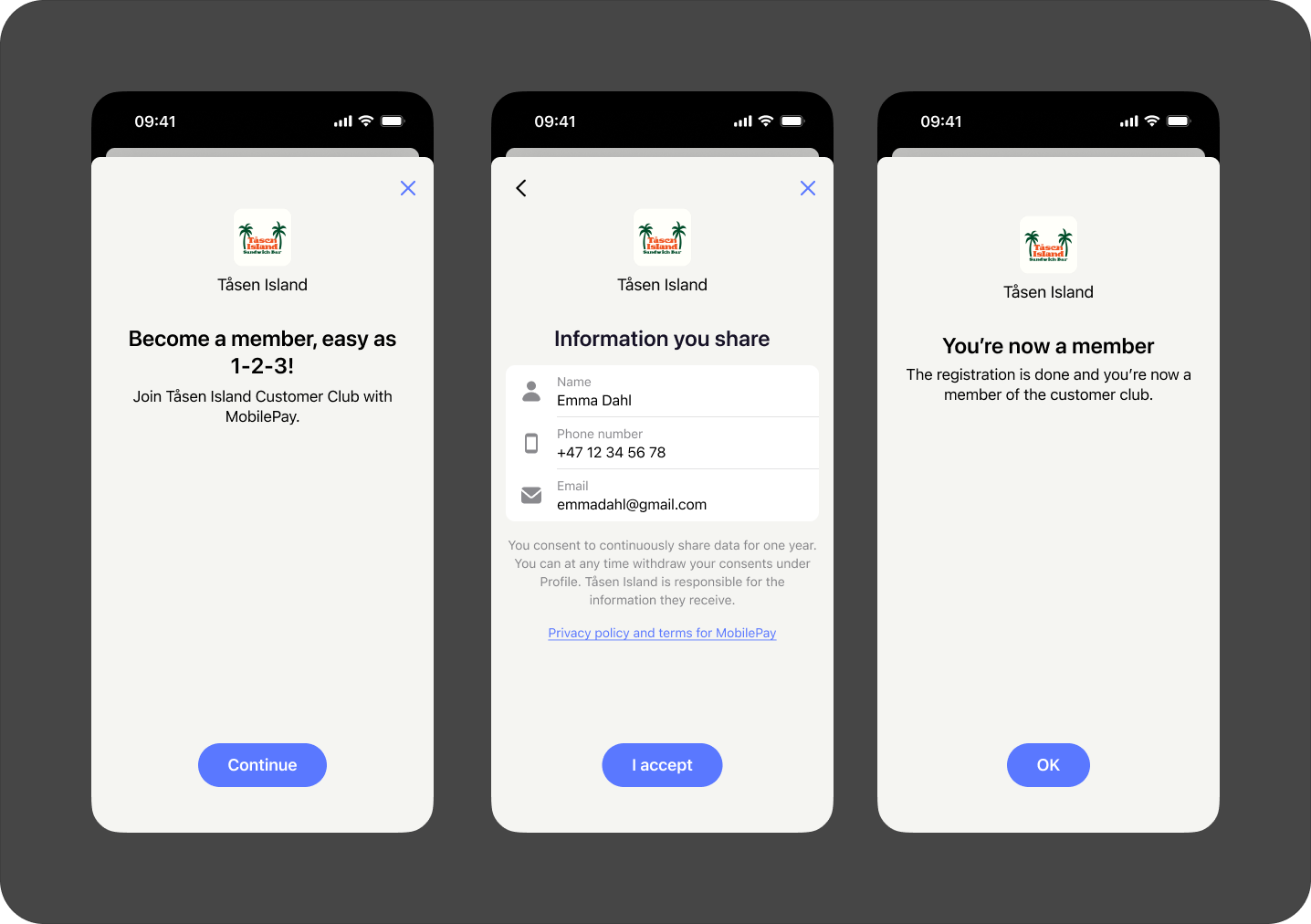
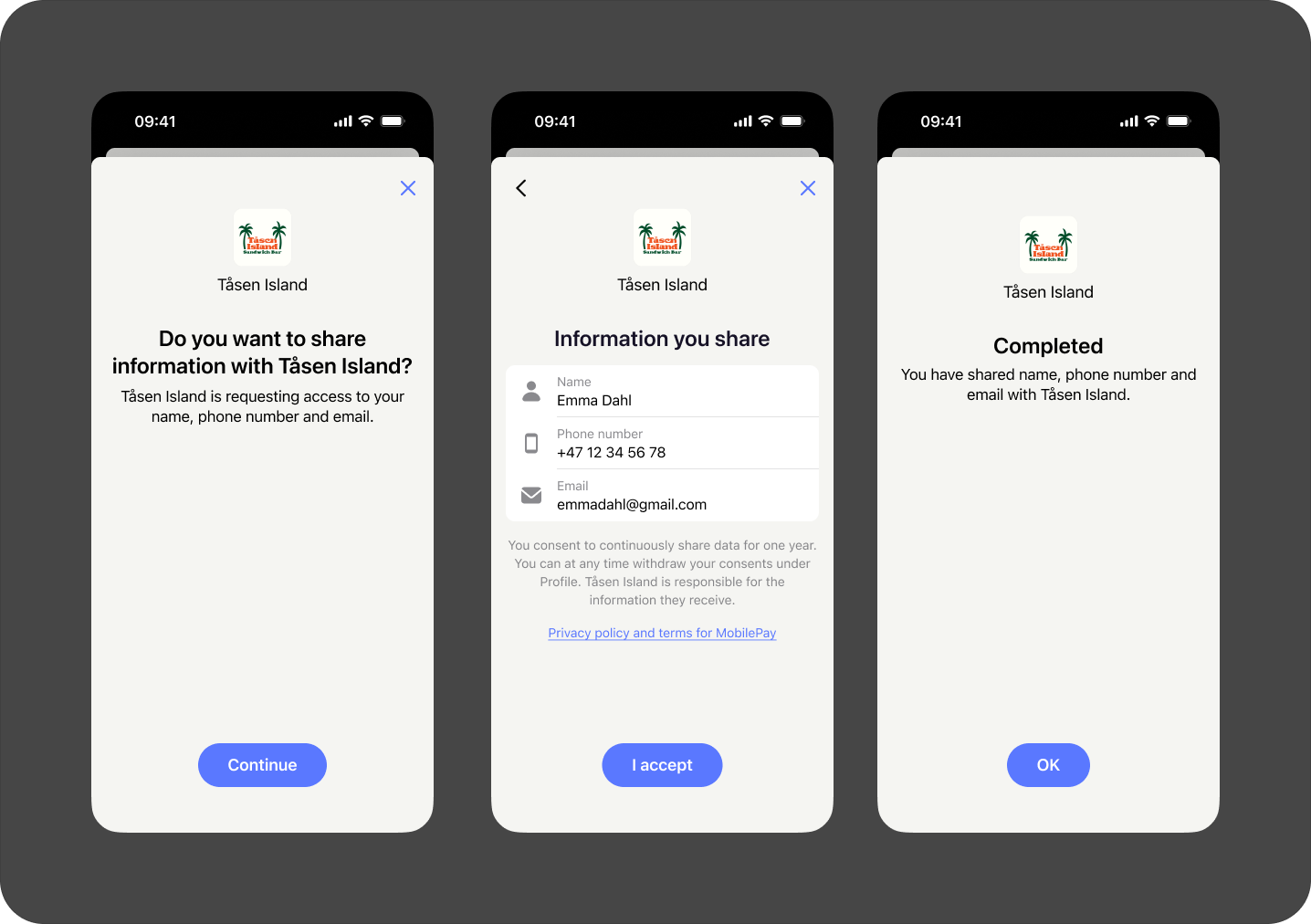
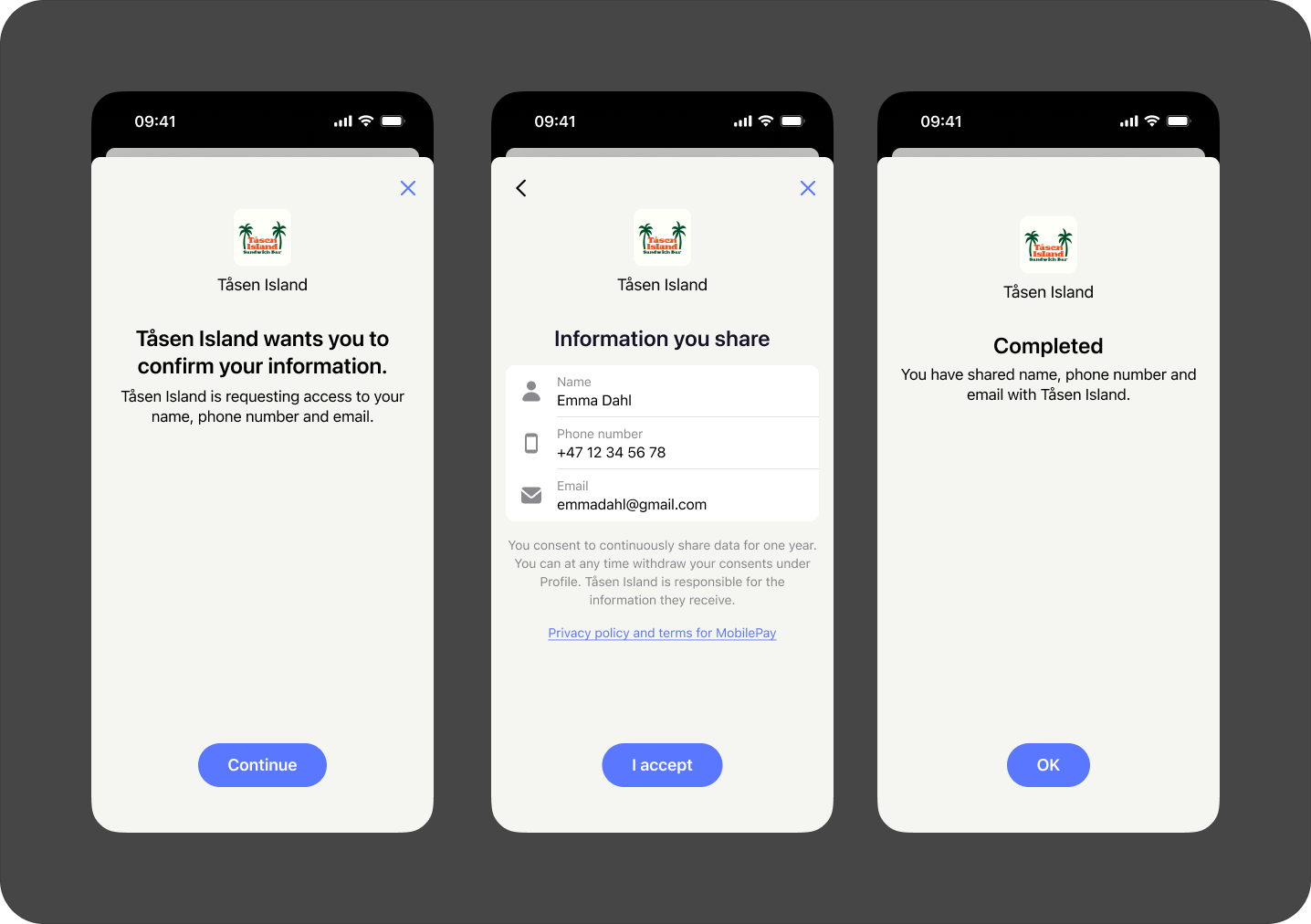
- Vipps
- MobilePay
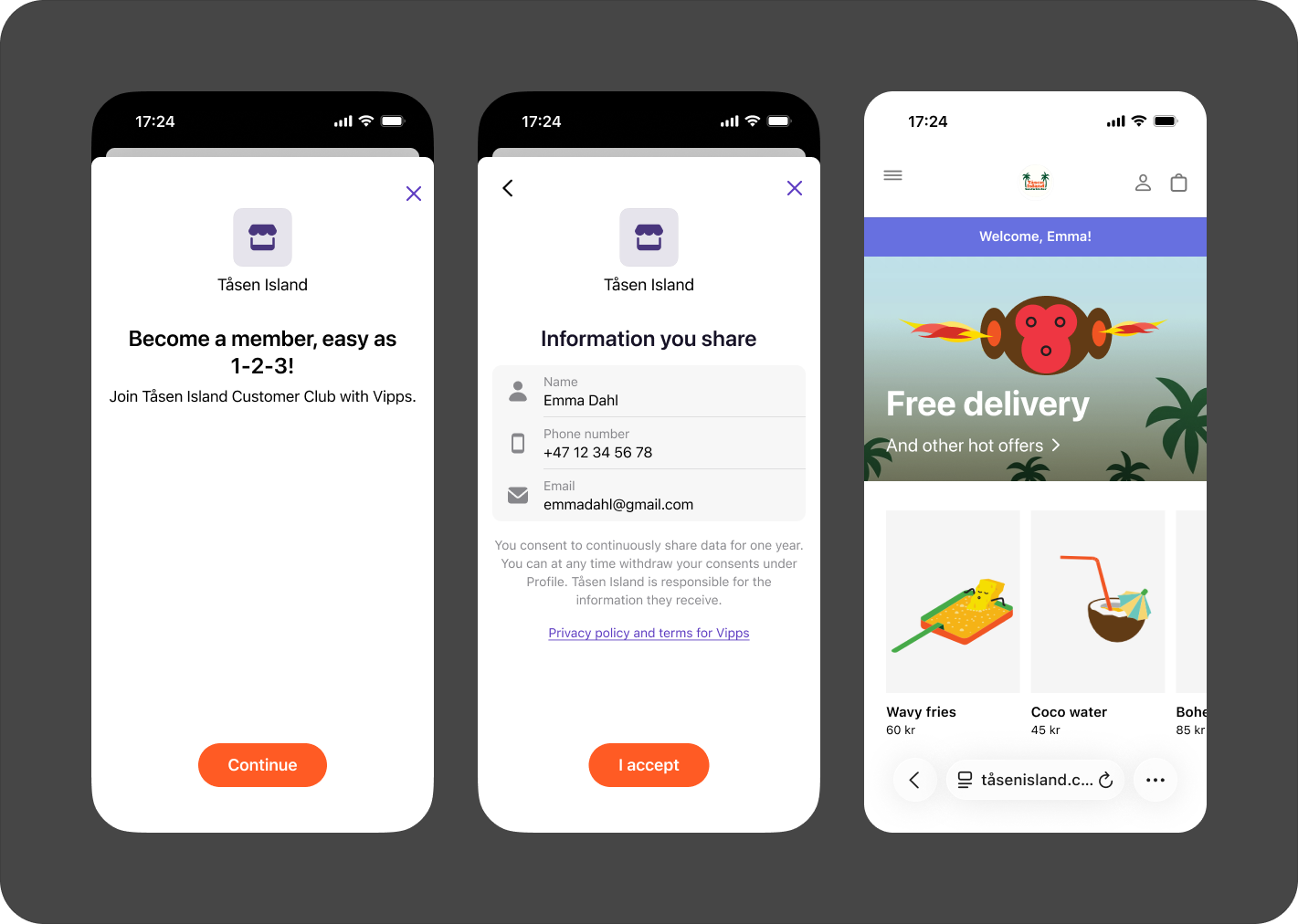
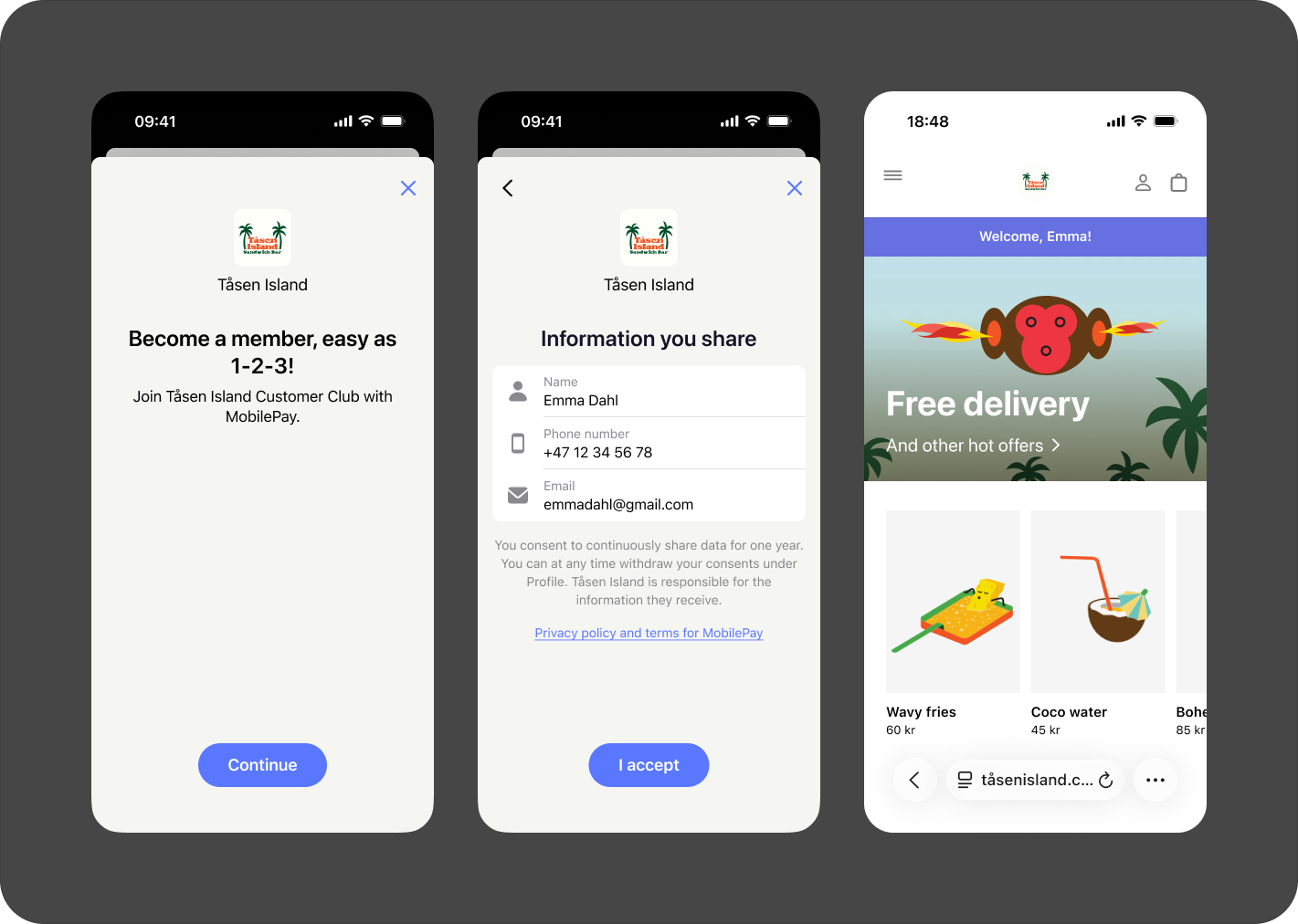
Alternatively, the merchant may redirect the user to the merchant's web page to finalize the flow (e.g., enable input of more information, accept terms and conditions, log the user in at their web page, show relevant information/offers or to continue to set up an agreement or completing a purchase). For example:
- Vipps
- MobilePay
For more illustrations, see How it works: Merchant-initiated login.
To get help with this from a partner, go to Find a partner and select the Customer Club in store solution.
Customization
Merchants can customize the login flow to suit their specific needs. Here are the available options:
- Binding message: As a security measure you can add a simple message or identifier that will help the user verify that they're accepting the correct login by seeing the message on both devices.
- Redirect to browser: Redirect users to a website once the login is successfully completed.
- Marketing consents: Use this extra step to collect consents needed for enrolling customers in your loyalty program.
- Merchant-initiated login texts: Select between different texts that we will display to the user during the flow.
Tailor the flow to fit your use case and create a seamless experience for your customers!
Complete login in the Vipps or MobilePay app
This flow is based on the Client-Initiated Backchannel Authentication (CIBA) standard. CIBA enables a Client to initiate the authentication of an end-user through out-of-band mechanisms.
- The Client shall make an "HTTP POST" request to the Backchannel Authentication Endpoint to ask for end-user authentication.
- Login will respond immediately with a unique identifier that identifies that authentication while it tries to authenticate the user in the background.
- The Client will receive the ID Token and Access Token by polling the token endpoint to get a response with the tokens.
Call by call (complete login in app)
-
Before all this, the merchant has fetched the OpenID configuration from the well-known endpoint and cached it. See .well-known
-
The merchant initiates a login by calling the
backchannel_authentication_endpointlisted in the OpenID configuration (fetched in the previous step).For details, see Authentication request (complete login in app).
Example request:
POST https://api.vipps.no/vipps-login-ciba/api/backchannel/authentication
Authorization: Basic asdkjhasdjhsad=
Content-Type: application/x-www-form-urlencoded
scope=name address openid&login_hint=urn:msisdn:{msisdn}&state=13821s837213bng26e2n61gege26Example response:
200 application/json
{
"auth_req_id": "VYGaaAMRkI6SyAm_uIywhxsN2K0",
"expires_in": 600,
"interval": 5
}The
intervalreturned is the minimum amount of time (in seconds) that the client must wait between polling requests to the token endpoint. Polling in this context means doing repeated HTTP requests with a delay between them. -
The merchant starts polling the
tokenendpoint listed in the OpenID configuration (fetched in step 0). Note that the polling interval should not exceed theintervalresponse parameter (in seconds) returned in the previous step.- For information about polling, see Information about polling.
- For an alternative to polling, see webhook events.
- For other details about the request, see Token request.
Example request:
POST https://api.vipps.no/access-management-1.0/access/oauth2/token
Authorization: Basic asdkjhasdjhsad=
Content-Type: application/x-www-form-urlencoded
grant_type=urn%3Aopenid%3Aparams%3Agrant-type%3Aciba&auth_req_id=VYGaaAMRkI6SyAm_uIywhxsN2K0Example pending response (Other possible error responses can be found in the CIBA standard):
HTTP/1.1 400 Bad Request
Content-Type: application/json;charset=UTF-8
{
"error": "authorization_pending",
"error_description": "The authorization request is still pending"
}The merchant should keep polling when it receives
authorization_pendingin the error response. After the user completes the login in the app, thetokenendpoint will give a successful response similar to the following example:HTTP/1.1 200 OK
Content-Type: application/json;charset=UTF-8{
"access_token": "ciba.W_IfBcSr-askdjhsakjhd",
"token_type": "Bearer",
"expires_in": 300,
"id_token": "eyaksjdhksajhdjkashdjksadjnn91283hedhn.eyasdkjhaskjdhskajhdkjhasdkjhaskjhdwqiuh"
} -
The merchant must do a GET to the
userinfoendpoint with the header:Authorization: Bearer {access_token}, using the access_token retrieved in step 2.For details see Userinfo request.
Example request:
GET https://api.vipps.no/vipps-userinfo-api/userinfo
Authorization: Bearer ciba.W_IfBcSr-askdjhsakjhdExample response:
HTTP/1.1 200 OK
{
"address": {
"address_type": "home",
"country": "NO",
"formatted": "jghj khhjhhkjh\n0603\nOSLO\nNO",
"postal_code": "0603",
"region": "OSLO",
"street_address": "jghj khhjhhkjh"
},
"family_name": "Heyerdahl",
"given_name": "Tor Fos",
"name": "Tor Fos Heyerdahl",
"other_addresses": [],
"sid": "qwieuhwqiuhdiuwqh",
"sub": "f350ef33-22e2-47d0-9f47-12345667"
}
Authentication request (complete login in app)
Standard definition: https://openid.net/specs/openid-client-initiated-backchannel-authentication-core-1_0.html#auth_request
The Backchannel Authentication Endpoint is listed as backchannel_authentication_endpoint in the configuration https://api.vipps.no/access-management-1.0/access/.well-known/openid-configuration.
Authentication
The following authentication methods are currently supported:
- client_secret_basic
- client_secret_post
The default token endpoint authentication method is client_secret_basic. It's possible to change the authentication method to client_secret_post through the business portal.
See: FAQ: How can I use client secret post for authentication.
The parameters are as follows:
| Parameter | Description |
|---|---|
login_hint (required) | The login_hint parameter includes two supported formats: one for mobile phone numbers and another for customer tokens. See login_hint. |
scope (required) | Supported scopes. See scope. |
binding_message (optional) | A human-readable identifier. See binding_message. |
requested_expiry (optional) | The requested expiration time. See requested_expiry. |
See sections below for more information.
The login_hint parameter (required)
Supported login hints:
-
Mobile phone numbers can be targeted by passing login hint as an MSISDN.
Login hint format:
login_hint=urn:msisdn:{msisdn}Example:
...&login_hint=urn:msisdn:4712345678&.... -
Customer token. This is supplied in the QR checked in webhook
Login hint format:
login_hint=urn:customer-token:{customerToken}Example:
...&login_hint=urn:customer-token:ezakjsedhiuqwhiuhd...
The scope parameter (required)
- We support the scopes listed at Scopes
- The legacy
nninscope is not supported, usenininstead.
Example: ...&scope=name address birthDate nin&...
The binding_message parameter (optional)
A human-readable identifier or message intended to be displayed on both the consumption device and the authentication device to interlock them together for the transaction by way of a visual cue for the end-user. It should not be used for attempting to convey other information.
The format possible for this field is limited to capital characters A-Z, numbers 0-9 and the character -. It must also be between 5 and 8 characters long. Regex: ^[A-Z0-9\\-]{5,8}$.
Read more about it in the Client-Initiated Backchannel Authentication Request.
Example: ....&binding_message=4MZ-CQ3&...
- Vipps
- MobilePay

The requested_expiry parameter (optional)
A positive integer representing the requested expiration time, in seconds, for the authentication. This will set the maximum time the authentication request is valid. The default value typically corresponds to ~10-15 minutes. Minimum is 60 seconds. Maximum is 900 seconds.
Responses (complete login in app)
Successful responses
Standard definition: OpenID Connect Client-Initiated Backchannel Authentication (CIBA): Successful Authentication Request Acknowledgement
Responses according to the standard. Note, we do return an interval parameter which indicates the minimum amount of time in seconds that the Client MUST wait between polling requests to the token endpoint.
Token request
Standard definition: OpenID Connect Client-Initiated Backchannel Authentication Flow: Token Request Using CIBA Grant Type
The responses from this endpoint are according to the standard.
- Note the required
grant_type:urn:openid:params:grant-type:ciba. - The access token can be used towards the standard OIDC userinfo endpoint.
Polling
- Long polling as described in the CIBA standard is currently not supported.
- Remember not to poll more often than indicated by the
intervalparameter, returned from the Authentication request (complete login in app). - See webhook events for an alternative to polling.
Error responses
In addition to the responses defined by the standard these responses might be returned:
429status responses: Too many login requests started towards the same user at the same time. Please respect theRetry-Afterheader returned.error_code=old_app: The user's Vipps or MobilePay app is outdated and does not support this login flow.error_code=invalid_user: No account exists, the user's account is not active, or the user is in some way not eligible to use this login flow currently e.g. U15 users.
Redirect to browser
This CIBA-related flow enables a Client to initiate the authentication of an end-user through out-of-band mechanisms and additionally facilitates the end user to be taken to the client's web page to finalize the flow.
- The Client shall make an "HTTP POST" request to the Backchannel Authentication Endpoint to ask for end-user authentication.
- The user, via their browser, will be redirected to the Client's
redirect_uriwhich enables the login to be completed.
Redirect-to-browser flow
Call by call (Redirect to browser)
-
Before all this, the merchant has fetched the OpenID configuration from the well-known endpoint and cached it. See .well-known.
-
The merchant initiates a login by calling the
backchannel_authentication_endpointlisted in the OpenID configuration (fetched in the previous step).For details see Authentication request (Redirect to browser).
Example request (the real payload will likely look different because of encoding):
POST https://api.vipps.no/vipps-login-ciba/api/backchannel/authentication
Authorization: Basic asdkjhasdjhsad=
Content-Type: application/x-www-form-urlencoded
requested_flow=login_to_webpage&scope=openid name address&login_hint=urn:msisdn:{msisdn}&redirect_uri=https://merchantwebpage.com/callbackExample response, the
auth_req_idshould be used to connect this login to a token response since the ID token should contain the sameauth_req_idvalue.200 application/json
{
"auth_req_id": "VYGaaAMRkI6SyAm_uIywhxsN2K0",
"expires_in": 600,
"interval": 5
}The
intervalreturned is the minimum amount of time (in seconds) that the client must wait between polling requests to the token endpoint. -
The user confirms the login and is then redirected to the
redirect_uripassed in the initial request 1. The redirect will contain acode:{redirect_uri}?code={code}. -
The merchant uses the code-parameter to obtain the login token. Perform a POST request towards the
{token_endpoint}withcode={code},grant_type=urn:vipps:params:grant-type:ciba-redirectin theapplication/x-www-form-urlencoded-body. This returns an ID token and an access token that can be used to fetch userinfo. The ID token is a JWS that must be validated, see ID Token. The merchant must validate that it contains theauth_req_idthey have previously received from step 1.Example request (the real payload will likely look different because of encoding):
POST https://api.vipps.no/access-management-1.0/access/oauth2/token
Authorization: Basic sadlksadkjasjdaksd
Content-Type: application/x-www-form-urlencoded
code=some-valid-code&grant_type=urn:vipps:params:grant-type:ciba-redirectExample response:
{
"access_token": "hel39XaKjGH5tkCvIENGPNbsSHz1DLKluOat4qP-A4.WyV61hCK1E2snVs1aOvjOWZOXOayZad0K-Qfo3lLzus",
"id_token": "eyJraWQiOiJwdWJsaWM6ZWUzNmQzZjUtMzkzNC00MDI5LTkyNmYtNzdmYTY1YmYwYjRiIiwiYWxnIjoiRVMyNTYifQ.eyJhdWQiOiJlZGRkYjMyZi01MDI4LTQzOTctYjBhYi1lOGVjZjIxOGZkYzIiLCJzdWIiOiI1MTY4ZWUwNi04NzFlLTQ2ZTYtOTQxZS0wMTAzYjk1NzA0OGUiLCJhdXRoUmVxSWQiOiI3QnpBWS1TYlZRSjM4Vi1VMEM3WjZrMjNfQ1kiLCJpc3MiOiJodHRwczpcL1wvZWNlNDZlYzQtNmY5Yy00ODliLThmZTUtMTQ2YTg5ZTExNjM1LnRlY2gtMDIubmV0XC9hY2Nlc3MtbWFuYWdlbWVudC0xLjBcL2FjY2Vzc1wvIiwiZXhwIjoxNjQzMTc5ODM3LCJpYXQiOjE2NDMxNzkyMzd9.iFvmdtRQVliAe91dBu_CZDfBD5I7WCbDTiDQxu4sOTApXFPb5EsSuEBEVfK_-14E7xjcfQLSMa6ZO06YvhRHAA",
"expires_in": 3599,
"scope": "openid",
"token_type": "bearer"
}Decoded ID token JWS example:
Header{
"kid": "public:ee36d3f5-3934-4029-926f-77fa65bf0b4b",
"alg": "ES256"
}Payload{
"aud": "edddb32f-5028-4397-b0ab-e8ecf218fdc2",
"sub": "5168ee06-871e-46e6-941e-0103b957048e",
"auth_req_id": "7BzAY-SbVQJ38V-U0C7Z6k23_CY",
"iss": "https://ece46ec4-6f9c-489b-8fe5-146a89e11635.tech-02.net/access-management-1.0/access/",
"exp": 1643179837,
"iat": 1643179237
} -
The merchant must do a GET to the
userinfoendpoint with the header:Authorization: Bearer {access_token}, using the access_token retrieved in step 3.For details see Userinfo request.
Example request:
GET https://api.vipps.no/vipps-userinfo-api/userinfo
Authorization: Bearer W_IfBcSr-askdjhsakjhdasdfggExample response:
HTTP/1.1 200 OK
{
"address": {
"address_type": "home",
"country": "NO",
"formatted": "jghj khhjhhkjh\n0603\nOSLO\nNO",
"postal_code": "0603",
"region": "OSLO",
"street_address": "jghj khhjhhkjh"
},
"family_name": "Heyerdahl",
"given_name": "Tor Fos",
"name": "Tor Fos Heyerdahl",
"other_addresses": [],
"sid": "qwieuhwqiuhdiuwqh",
"sub": "f350ef33-22e2-47d0-9f47-12345667"
}
Authentication request (Redirect to browser)
The Backchannel Authentication Endpoint is listed as backchannel_authentication_endpoint in the configuration https://api.vipps.no/access-management-1.0/access/.well-known/openid-configuration.
Authentication is the same as authentication request for complete login from the app.
with the addition of redirect_uri, which is the redirect URL that the user agent is redirected to after finishing a login.
It must be https in the production environment. Example: ...&redirect_uri=https://merchant.com/callback&...
Error responses are same as authentication request for complete login from the app.
Webhook events
To avoid frequent polling of the token endpoint, register a webhook to be notified via a login.merchant-initiated.ping.v1 event when a login is completed.
The payload will contain:
| Name | Type | Description |
|---|---|---|
auth_req_id | String | The auth_req_id that identifies the login. |
Example:
{
"auth_req_id": "qwieuhwqiuhdiuwqh123"
}
We support up to 25 webhook registrations per sales unit (MSN) for each event type.
Webhooks call by call
- The merchant subscribes to the
login.merchant-initiated.ping.v1event. - The merchant initiates a login by calling the
backchannel_authentication_endpoint. - The user confirms the login.
- The merchant receives a webhook event with the
auth_req_idthat identifies the login. - The merchant calls the token endpoint to get the tokens.
Although the Redirect to browser flow also allows for receiving webhook notifications for logins, it has a key limitation:
- The token endpoint can be called only once per authentication. Doing the token exchange based on the webhook will prevent doing the token exchange based on the browser redirect which might not be intended.
Merchant-initiated login marketing consents
If you are just starting out, review the Collecting consents section.
For Client-Initiated Backchannel Authentication (CIBA), it's possible to initiate the authentication of an end-user through out-of-band mechanisms and collect consents on behalf of the merchant.
- The Client shall make an "HTTP POST" request to the Backchannel Authentication Endpoint with scope
delegatedConsentsto ask for end-user authentication and on behalf of the merchant consents. - Login will respond immediately with a unique identifier that identifies that authentication while it tries to authenticate the user in the background, along with collecting consents.
- The Client will receive the ID Token and Access Token by polling the token endpoint to get a response with the tokens.
- Token can be used by the Client to retrieve information about the user through the
userinfoendpoint, this response will also contain the consents that are approved/declined by the user.
Requesting consents on behalf of the merchant is also available for redirect to browser, by adding scope delegatedConsents to the initial request (1).
Call by call (Merchant-initiated login with marketing consents)
-
Before all this, the merchant has fetched the OpenID configuration from the well-known endpoint and cached it. See .well-known
-
The merchant initiates a login by calling the
backchannel_authentication_endpointlisted in the OpenID configuration (fetched in the previous step). Use scopedelegatedConsents.For details, see authentication request for complete login from the app.
Example request:
POST https://api.vipps.no/vipps-login-ciba/api/backchannel/authentication
Authorization: Basic asdkjhasdjhsad=
Content-Type: application/x-www-form-urlencoded
scope=name delegatedConsents openid&login_hint=urn:msisdn:{msisdn}&state=13821s837213bng26e2n61gege26Example response:
200 application/json
{
"auth_req_id": "VYGaaAMRkI6SyAm_uIywhxsN2K0",
"expires_in": 600,
"interval": 5
}The
intervalreturned is the minimum amount of time (in seconds) that the client must wait between polling requests to the token endpoint. -
The merchant starts polling the
tokenendpoint listed in the OpenID configuration (fetched in step 0). Note that the polling interval should not exceed theintervalresponse parameter (in seconds) returned in the previous step.- For information about polling, see Information about polling.
- For other details about the request, see Token request.
Polling in this context means doing repeated HTTP requests with a delay between them.
Example request:
POST https://api.vipps.no/access-management-1.0/access/oauth2/token
Authorization: Basic asdkjhasdjhsad=
Content-Type: application/x-www-form-urlencoded
grant_type=urn%3Aopenid%3Aparams%3Agrant-type%3Aciba&auth_req_id=VYGaaAMRkI6SyAm_uIywhxsN2K0Example pending response (Other possible error responses can be found in the CIBA standard):
HTTP/1.1 400 Bad Request
Content-Type: application/json;charset=UTF-8
{
"error": "authorization_pending",
"error_description": "The authorization request is still pending"
}The merchant should keep polling when it receives
authorization_pendingin the error response. After the user completes the login in the app, thetokenendpoint will give a successful response similar to the following example:HTTP/1.1 200 OK
Content-Type: application/json;charset=UTF-8
{
"access_token": "ciba.W_IfBcSr-askdjhsakjhd",
"token_type": "Bearer",
"expires_in": 300,
"id_token": "eyaksjdhksajhdjkashdjksadjnn91283hedhn.eyasdkjhaskjdhskajhdkjhasdkjhaskjhdwqiuh"
} -
The merchant must do a GET to the
userinfoendpoint with the header:Authorization: Bearer {access_token}, using the access_token retrieved in step 2.For details see Userinfo request.
Example request:
GET https://api.vipps.no/vipps-userinfo-api/userinfo
Authorization: Bearer ciba.W_IfBcSr-askdjhsakjhdExample response:
HTTP/1.1 200 OK
{
"family_name": "Heyerdahl",
"given_name": "Tor Fos",
"name": "Tor Fos Heyerdahl",
"other_addresses": [],
"sid": "qwieuhwqiuhdiuwqh",
"sub": "f350ef33-22e2-47d0-9f47-12345667"
"delegatedConsents" : {
"language" : "EN",
"heading" : "Give consent",
"text" : "oidc-testclient wants to send you relevant offers through their digital channels.",
"termsDescription" : "By confirming, you accept oidc-testclient's terms of membership. They are responsible for processing the consents. You can withdraw them at any time on their website.",
"confirmConsentButtonText" : "Confirm",
"links" : {
"termsLinkText" : "Read the terms of use.",
"termsLinkUrl" : "http://vippsmobilepay.com/legal/terms-and-conditions",
"privacyStatementLinkText" : "Read the privacy policy.",
"privacyStatementLinkUrl" : "https://vippsmobilepay.com/terms-privacy"
},
"timeOfConsent" : "2022-11-23T11:40:13Z",
"consents" : [ {
"id" : "email",
"accepted" : true,
"required" : true,
"textDisplayedToUser" : "Receive offers via email"
}, {
"id" : "sms",
"accepted" : true,
"required" : false,
"textDisplayedToUser" : "Receive offers via SMS"
}, {
"id" : "digital",
"accepted" : true,
"required" : false,
"textDisplayedToUser" : "I would like to receive digital marketing"
}, {
"id" : "personal",
"accepted" : true,
"required" : false,
"textDisplayedToUser" : "Get customized offers"
} ]
}
}
Authentication request (Merchant-initiated login with marketing consents)
Required parameters are listed in Authentication request (complete login in app) and Authentication request (Redirect to browser).
| Section | Description |
|---|---|
| Error responses | See: Error responses. |
| Successful responses | See: Successful responses for login from phone number |
| Token request | See: Token request login from phone number |
| Polling | See: Polling login from phone number |
Merchant-initiated login texts
A merchant can select between different texts that we will display to the user during the flow. The text type can be changed on the business portal, as described in How to configure text for merchant-initiated login flow.
You can select from these options:
- Join customer club
- Share information
- Confirm information
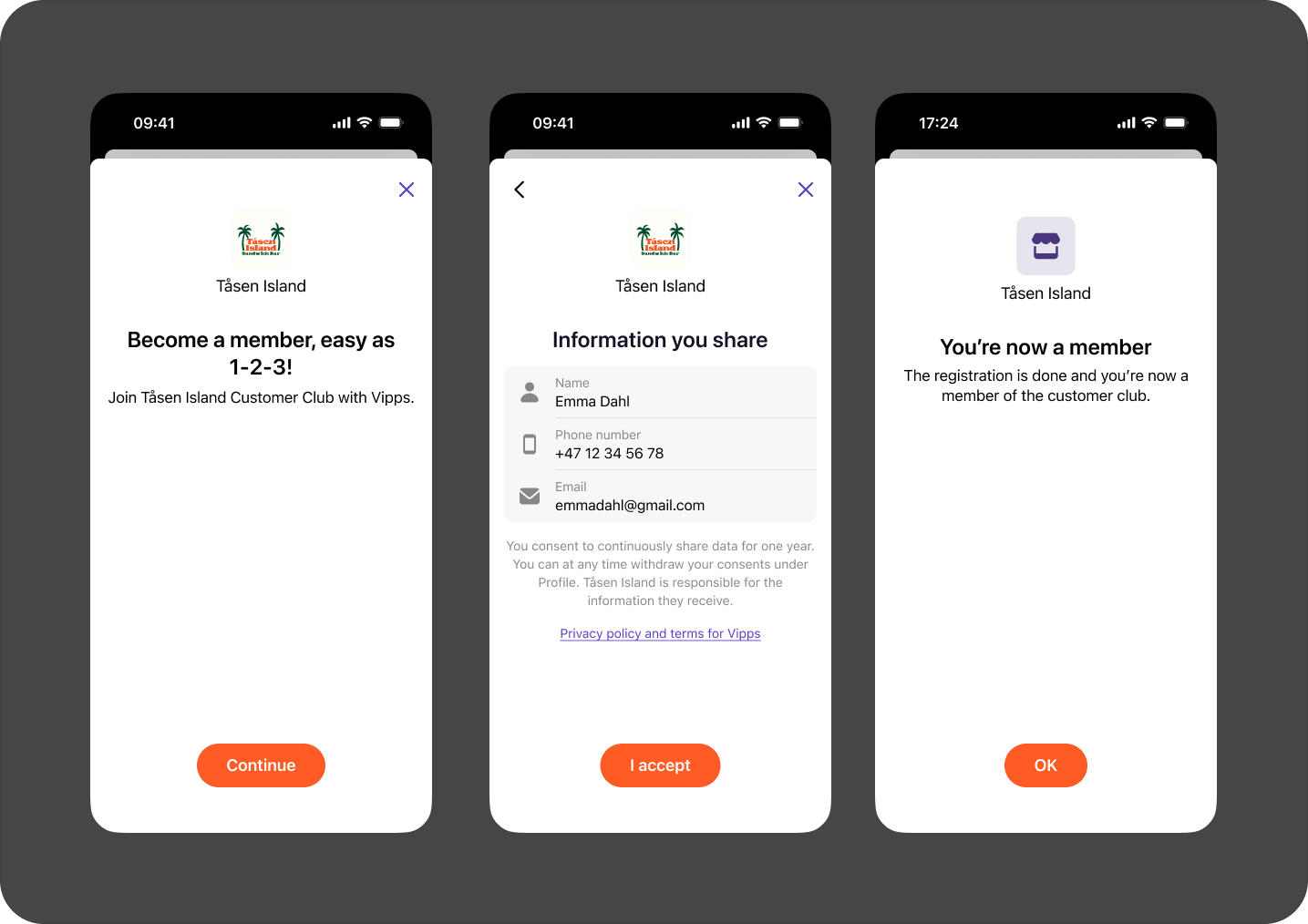
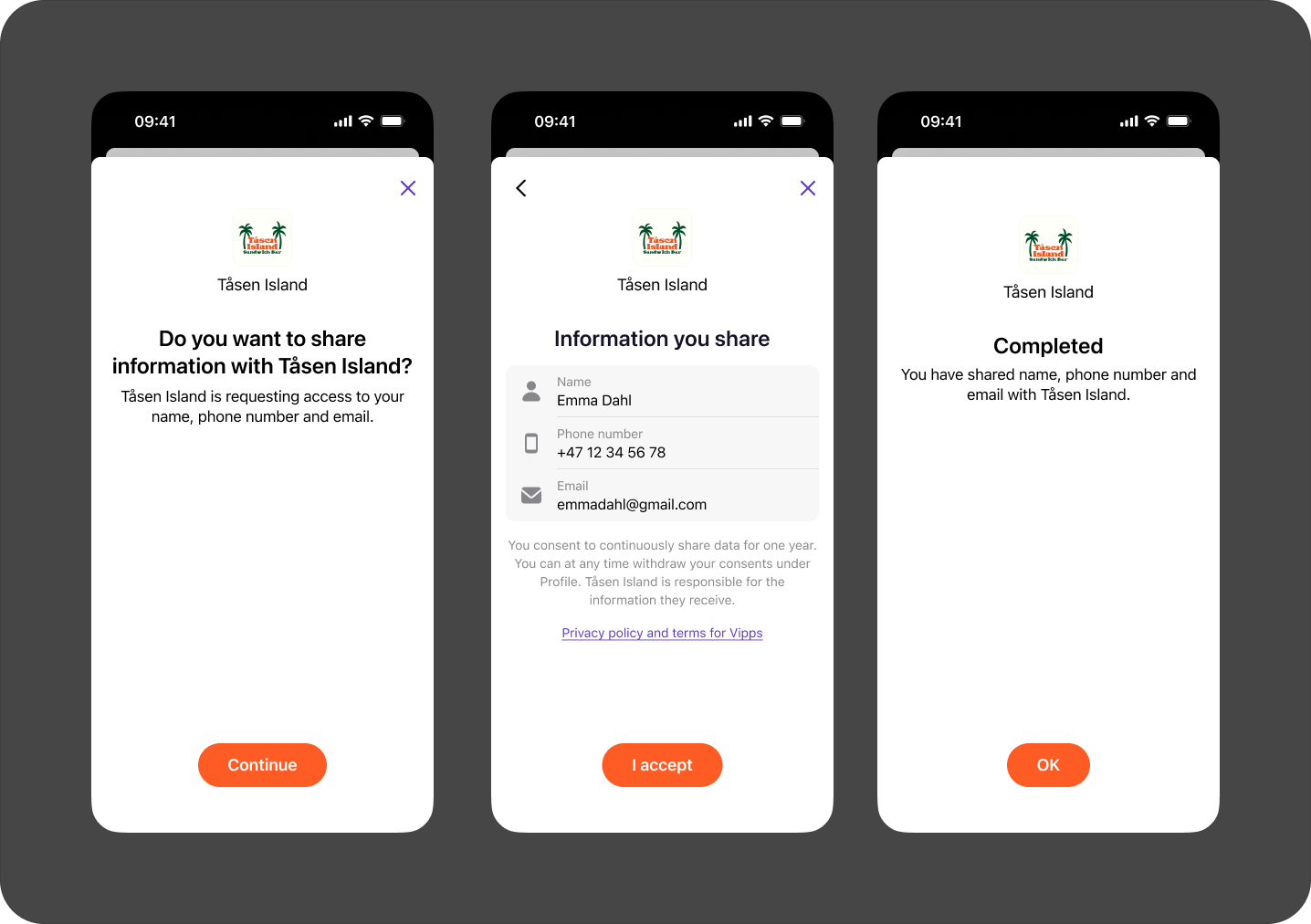
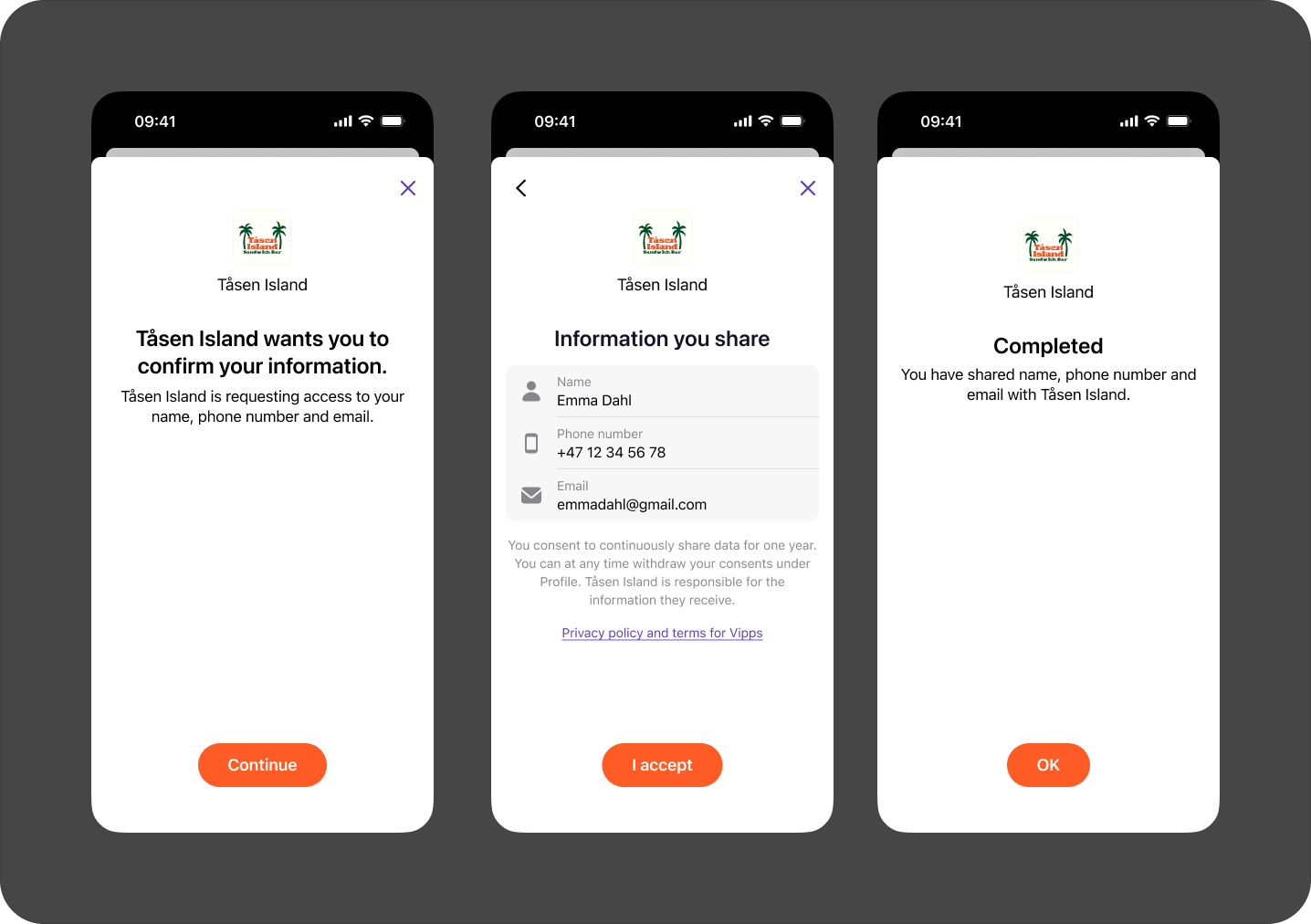
The following are examples of how these will look in the app:
- Vipps
- MobilePay
Join customer club
Share information
Confirm information
Join customer club
Share information
Confirm information
Check if user exists
A merchant can check if a user exists in Vipps MobilePay before initiating an authentication.
This is done with the POST:/vipps-login-ciba/api/v1/user-exists endpoint.
Provide the login-hint in the body.
For example: login_hint=urn:msisdn:4712345678.
Example request:
POST https://api.vipps.no/vipps-login-ciba/api/v1/user-exists
Authorization: Basic asdkjhasdjhsad=
Content-Type: application/x-www-form-urlencoded
login_hint=urn:msisdn:{msisdn}
Example response:
{ "exists": true }
 or MobilePay
or MobilePay  app.
By clicking the push message, the user is taken to their Vipps or MobilePay app to confirm the authentication/registration.
app.
By clicking the push message, the user is taken to their Vipps or MobilePay app to confirm the authentication/registration.